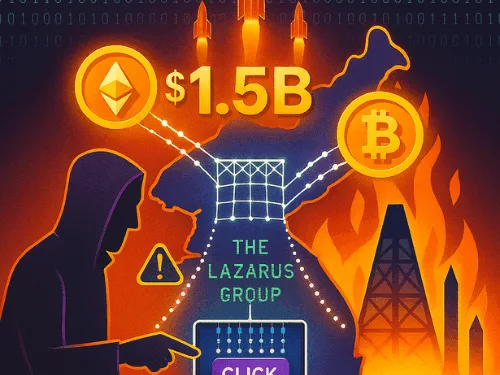
On February 21, 2025, North Korea pulled off the largest cryptocurrency theft in history, draining $1.5 billion from Dubai-based exchange Bybit in a single strike. The Bybit hack Lazarus Group operation exposed how North Korea turns stolen crypto into nuclear funding, bypassing sanctions in plain sight. Within 48 hours, state-sponsored hackers laundered over $160 million through decentralised networks, proving how nation-states now weaponise cryptocurrency to finance nuclear programs and sidestep international sanctions. The Bybit exploit is more than just a cybercrime milestone. It signals a new form of economic warfare, one where rogue states exploit blockchain’s borderless design to fund weapons of mass destruction while dodging traditional financial oversight.
The Anatomy of a Bybit Hack Lazarus Group Attack
The Lazarus Group, operating under North Korea’s Reconnaissance General Bureau (RGB), compromised Safe{Wallet}, a multi-signature wallet solution used to authorise Bybit’s cold storage transfers.
Hackers injected malicious code into the Safe{Wallet} interface via a compromised developer machine. When Bybit’s signers approved what appeared to be routine transfers, they inadvertently granted attackers full control over the exchange’s cold wallet contracts. Within minutes, over 401,000 ETH and other assets disappeared. Days later, the FBI attributed the breach to Lazarus under the codename “TraderTraitor”.
From Isolation to Innovation: The Geopolitics of Cyber Theft
North Korea’s rise as a crypto superpower stems directly from sanctions pressure. After the 2017 nuclear test, global sanctions cut off trade and financing options. By 2022, North Korean hackers stole a record $1.7 billion in crypto to fill state coffers. Cyber theft now funds roughly 50% of North Korea’s foreign currency needs, much of it channelled into nuclear and missile programs. Experts estimate the regime deploys 6,000–7,000 operatives across Lazarus, Kimsuky, and Andariel groups.
As cyber expert Geoff White explained: “North Korea ran out of money it can’t trade or borrow. So government hackers are sent out on missions to steal foreign currency”.
DeFi as a Weapon of War
The Bybit hack Lazarus Group laundering strategy relied heavily on DeFi protocols. Analysts tracked over $386 million routed through THORChain, ParaSwap, and PancakeSwap, with $263 million funnelled through PancakeSwap alone.
Unlike centralised mixers like Tornado Cash, now sanctioned DeFi protocols lack KYC requirements, making them ideal laundering pipelines. The hackers also used cross-chain bridges to obfuscate trails, moving value seamlessly across blockchains. As sanctions close one loophole, North Korea innovates another, turning open DeFi infrastructure into a tool for illicit finance.
The $7 Billion Cross-Chain Crime Empire
The Bybit theft is just the latest episode in Lazarus’s multi-billion-dollar cross-chain campaign. Between 2022 and 2023, the group stole $900 million, feeding into a $7 billion laundering scheme.
In 2023 and 2024 alone, Lazarus hit Atomic Wallet ($100M), Stake.com ($41M), and CoinEx ($31M). Analysts also found Bybit funds commingled with January 2025’s $29M Phemex hack, exposing coordinated multi-target campaigns.
Nuclear Ambitions Paid in Crypto
The strategic purpose of these hacks is clear: funding North Korea’s nuclear program. UN reports estimate cyber operations have generated $2 billion for WMD programs since 2017.
Treasury officials warn that stolen crypto directly fuels missile development. “The DPRK’s use of virtual currency for unlawful WMD programs directly threatens international security,” said Treasury Under Secretary Brian Nelson. This isn’t petty theft; it’s digital warfare financing weapons capable of destabilising Asia and beyond.
Industrial-Scale Laundering
Blockchain forensics revealed Lazarus operatives working around the clock in shifts to push Bybit’s stolen funds through decentralised platforms. Analysts observed 24/7 laundering cycles, with roughly 20% of funds “going dark” within weeks, effectively unrecoverable. Elliptic co-founder Dr Tom Robinson noted: “Every moment is crucial for the hackers. They show a level of sophistication far beyond traditional organised crime.”
The Arms Race Escalates
Bybit responded by launching the “Lazarus Bounty” program, offering $140 million in rewards for intelligence leading to fund recovery. Over 20 participants earned $4 million for tracing $40 million of stolen assets, but experts doubt most funds will ever be recovered.
The Bybit hack Lazarus Group attack highlights a new imbalance: decentralised finance protocols designed for openness are being bent into weapons by nation-states with near-limitless motivation.
Author’s Thoughts
The Bybit heist is more than the biggest crypto hack; it’s the clearest sign yet that cryptocurrency is now a battlefield in international conflict. The Lazarus Group’s ability to turn DeFi into a laundering machine shows how global rules written for banks don’t work on blockchains.
What alarms me most is not just the scale of theft, but the direct link between stolen crypto and nuclear weapons. Each click on a malicious signature doesn’t just drain digital wallets; it potentially funds missiles pointed at Seoul, Tokyo, or even Washington. Unless the international community adapts, the next front in global security won’t be fought in banks or trade routes, but on decentralised ledgers. The Bybit hack forces us to accept an uncomfortable truth: crypto crime is now statecraft.